How DOMA Achieves
HIPAA Compliance
DOMA is compliant with HIPAA (Health Insurance Portability and Accountability Act of 1996) regulation protecting private health information records.
About HIPAA Compliance
Who is required to comply with HIPAA?
According to HIPAA, any Covered Entity and Business Associates that use and store PHI must ensure its safety throughout its handling. It is required that any reasonable threats to the security of PHI be protected against, including physical, technical, and administrative threats.
You can learn more about HIPAA on the US Department of Health & Human Services website.
HIPAA Regulations protect private health information records by requiring:
HIPAA’s rules all center around Protected Health Information (PHI) and Electronic Protected Health Information (ePHI). PHI is individually identifiable information that centers around past, present, and future sensitive patient health information.
This includes:
- Medical Records
- Diagnoses
- Treatments
- Prescriptions
- Test Results
- As well as other Personally Identifiable Information (PII)
HIPAA Compliance at DOMA
We follow the HIPAA Regulations for safeguarding Protected Health Information (PHI) and Personal Identifiable Information (PII) throughout the handling of your documents.
In addition to extensive employee training, we make facility security a priority. Conversion Rooms are restricted, requiring key-card entry. In our Secure Document Conversion Rooms, cell phones, and all other forms of recording devices are prohibited, further protecting PII and PHI.
Employees undergo training in 12-month cycles, which includes:
- HIPAA
- PII
- PHI
- Cybersecurity Best Practices
- Password Security
- Facility Security
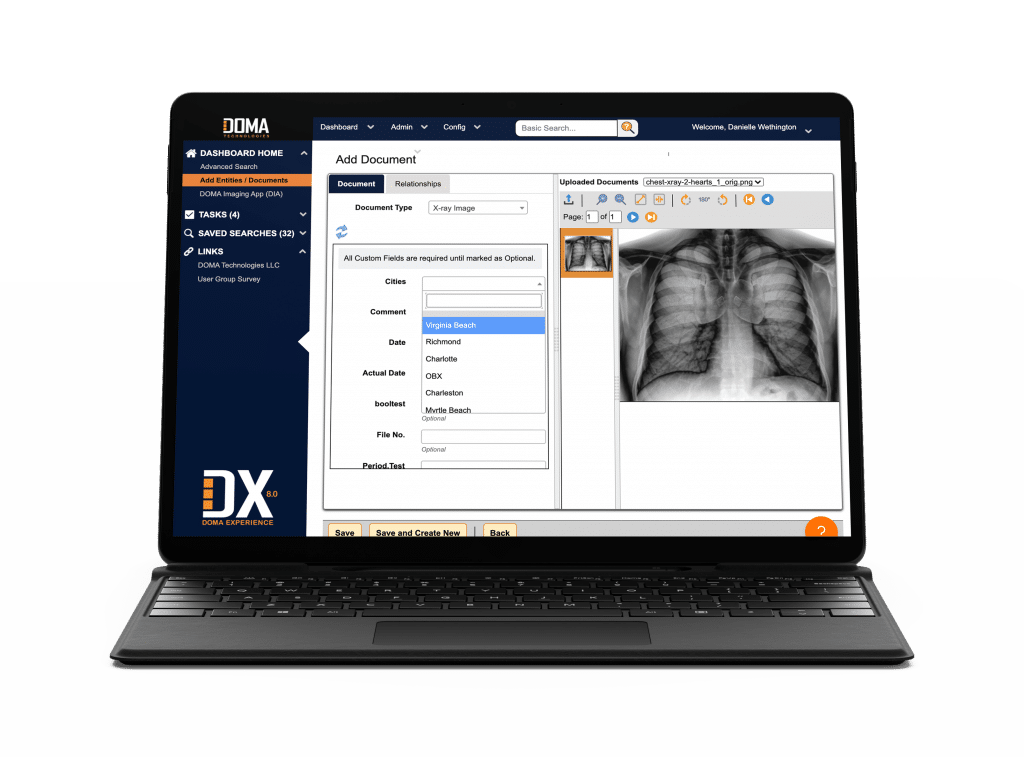
HIPAA Compliant Software Platform
DX Engage was built from the ground up to be secure
When you use our software as your Content Services Platform (CSP), you can rest easy knowing our platform is HIPAA compliant. Our DOMA DX software incorporates the following protocols to ensure your data is safe:
- Multi-Factor User Authentication
- Access Management, such as Time-Outs
- High-level Encryption
- Regular Patches
- Proactive Threat Protection
- Audit Trails
- Physical Security (Within DOMA)
- Backup, Disaster Recovery, & Version Control